MDM wins over GPO 🎤 check 1-2-1-2
But does it always?
There are a lot of caveats and exceptions, although this just expected to work out of the box. Microsoft's own article warns us that not all settings are equal.

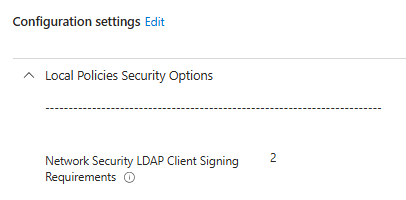
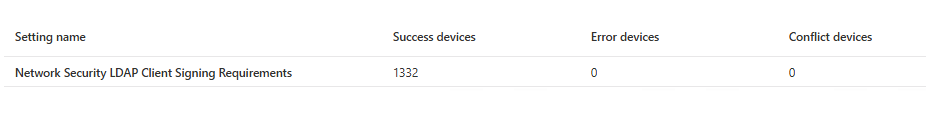
One of them happens to be the LDAP signing. But this was a tricky one to figure out. First Defender's compliance report for this security configuration started to light up. Intune was still reporting that the configuration was applied to all devices without any errors.
No conflicts either...
Log Analytics to the rescue
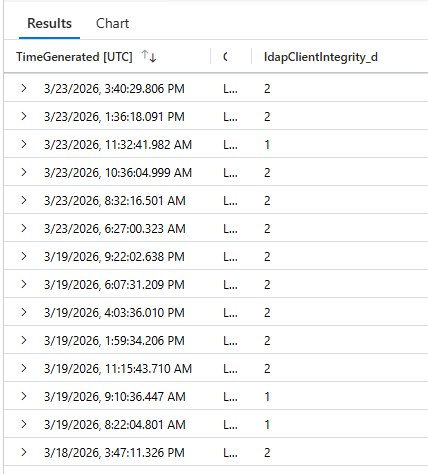
It's a good thing to have a script that runs on the endpoints periodically (mine does this every hour) and uploads various data points to a custom log (_CL) table. Damien has an excellent write up about Log Analytics in his series here.
I added this specific registry entry to be collected into log analytics to see if this was one of the flukes Defender has with some settings at times. Interestingly enough after about two weeks the pattern was that the value is flipping back and forth between 1 and 2. (I tried a funny title) 😄
Okay, the Intune Policy is there and configured and isn't conflicting.
Oh, but wait
These devices are in a hybrid environment... What about GPOs?
Bingo... There was indeed a setting for this in a GPO. It was configured to set this value to 1. So every refresh of group policies (I think the default is 90 minutes) this was set to 1. In turn. when IME did the sync, it switched to 2. When the reporting script ran it correctly reported the momentary value.
Et voilá there's the graph that shows the value over time:
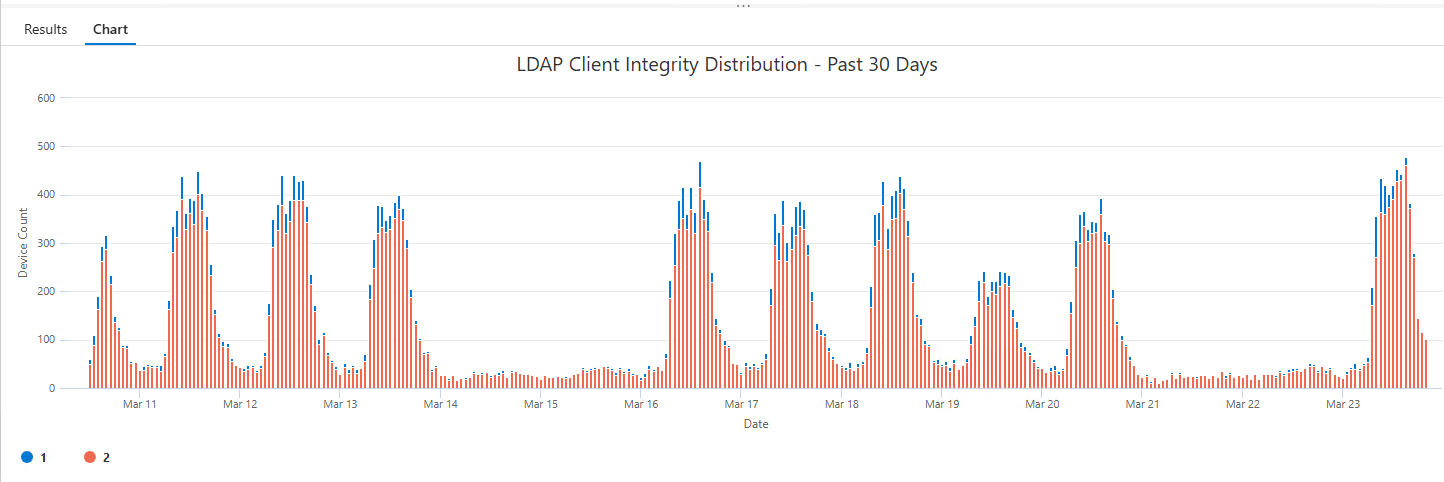
Now it's just the wait for Defender to re-send the daily reports and all should be in the green!